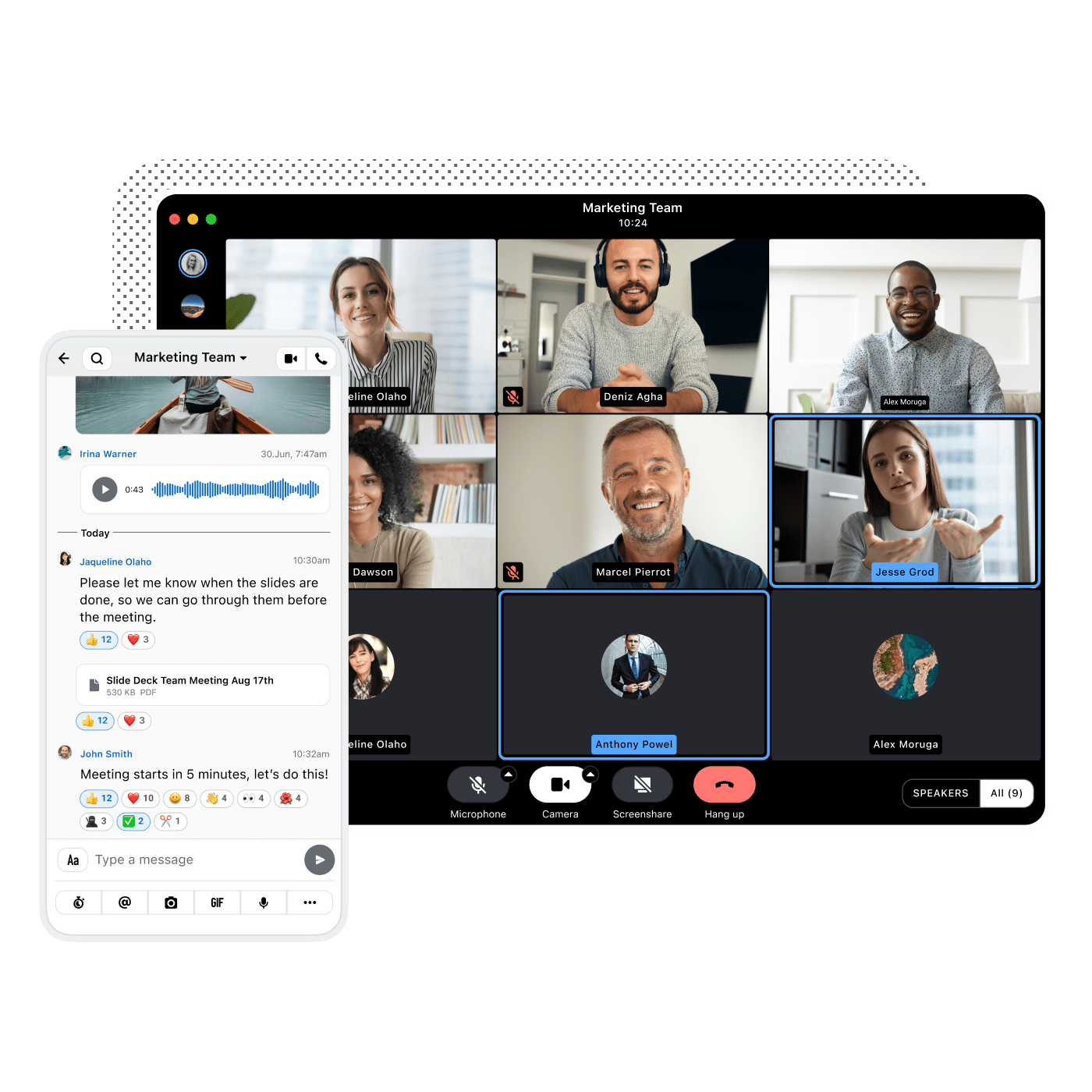
Wire and EBCONT Partner to Deliver Secure, Compliant Communication for Europe’s Public Sector and Infrastructure
Wire and EBCONT have joined forces to deliver secure, sovereign communication for public institutions and critical infrastructure in Europe. Learn...