Canada’s C-2 Bill Is The Latest Challenge to Digital Sovereignty
Canada’s proposed Bill C-2 quietly introduces one of the most far-reaching digital surveillance regimes in the democratic world. Disguised as a...

Canada’s proposed Bill C-2 quietly introduces one of the most far-reaching digital surveillance regimes in the democratic world. Disguised as a...

When WeTransfer quietly expanded its terms of service to allow AI model training on user-uploaded files, public backlash was swift and fierce. Within...
The UK MoD data leak wasn’t just a breach, it was a failure of trust, tech, and systems. This story reveals what’s at stake when lives and public...
The CLOUD Act allows U.S. authorities to access data stored in the EU, putting it in direct conflict with GDPR. Learn how this impacts data...

Explore how Europe’s digital sovereignty is undermined by Big Tech, encryption backdoors, and chat control. Insights from Tuta’s Hanna Bozakov on...

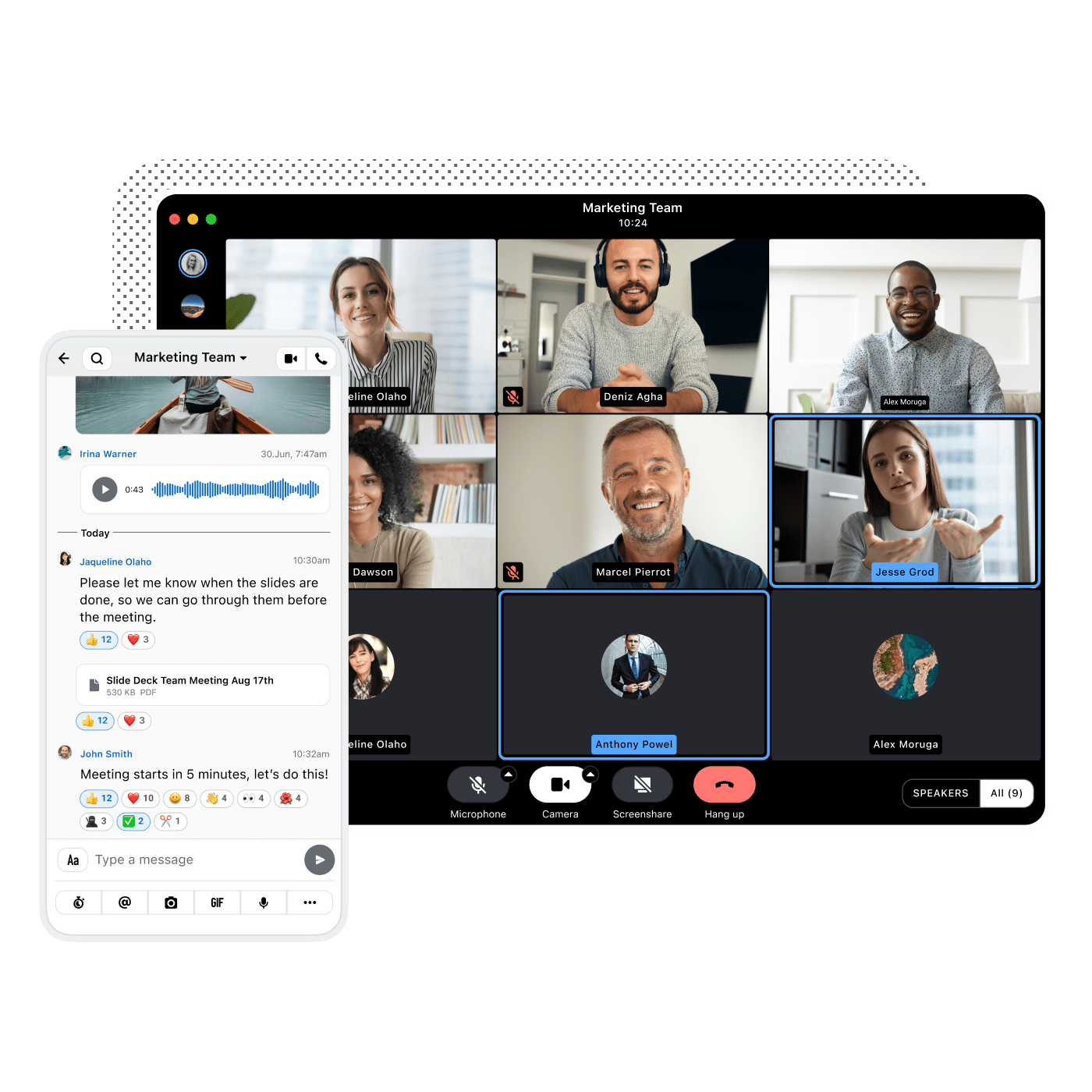
Despite prioritizing encryption and EU data hosting, European organizations still rely on US platforms like Microsoft Teams. Explore the four key...

Despite strong regulation, only 16% of tech and policy leaders believe Europe will achieve digital sovereignty. Discover what’s holding organizations...
In a cyberattack, your primary networks may go dark. Learn why fallback communication channels are essential for crisis continuity, resilience and...

Explore how NIS2 regulations are reshaping crisis communication and why end-to-end encryption, traceability, and fallback channels are now essential...