New Wire Teams Upgrade: Easy Transition from Personal to Team Accounts
Wire introduces a seamless upgrade process from personal to Teams accounts, offering enhanced collaboration features and invisible end-to-end...
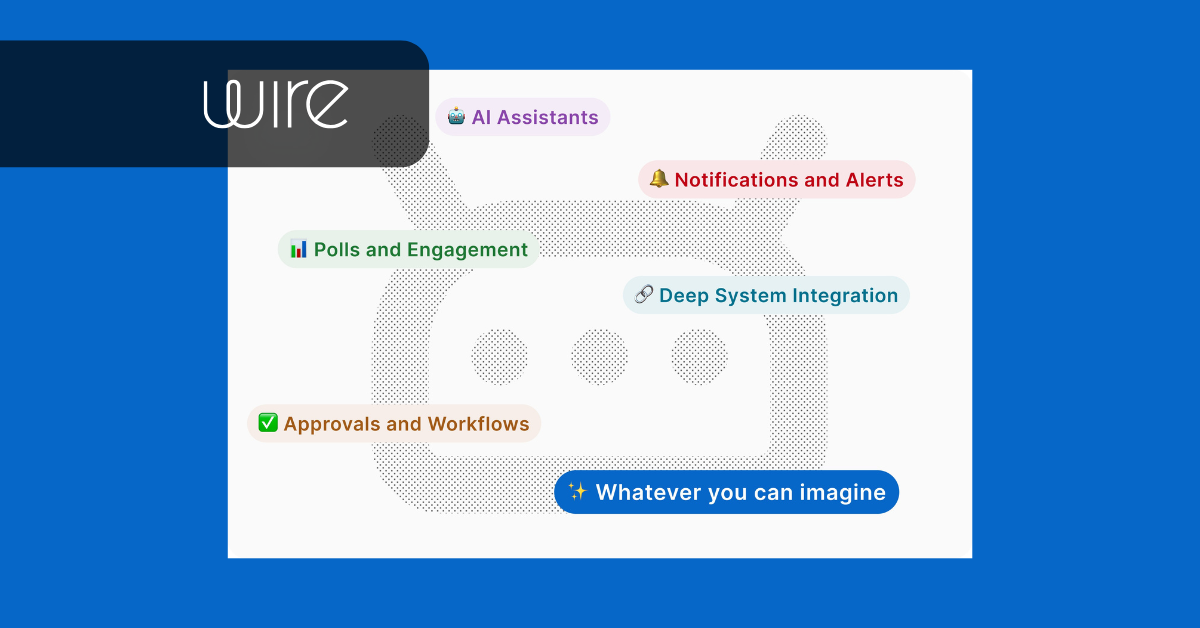
Discover the Wire Integrations SDK, a groundbreaking platform that empowers developers to create secure collaboration ecosystems with end-to-end encryption.
Modern collaboration software has evolved along two primary architectural paths. On one side are mainstream collaboration platforms that prioritize extensibility and integration but rely on centralized trust models. On the other are secure messaging applications that implement end-to-end encryption (E2EE), typically designed as closed communication systems rather than extensible development platforms.
The Wire Integration SDK represents a third architectural model: a self-contained, managed developer runtime that, in conjunction with the Wire backend, handles encryption, event routing, and storage, freeing developers to focus on collaboration logic rather than cryptographic infrastructure, which is built on emerging IETF standard Messaging Layer Security (MLS), which serves as the foundation of a secure collaboration ecosystem.Understanding why this change is so important requires examining how SDKs are typically structured across the collaboration landscape.
Developer ecosystems around mainstream collaboration platforms, such as Slack and Microsoft Teams, are designed around a centralized service architecture.
In these systems, the collaboration platform itself provides:
The SDKs exposed to developers function primarily as integration toolkits that allow external applications to interact with the platform via APIs.
Typical capabilities include:
From an architectural perspective, these SDKs are extensions of a hosted collaboration service, not foundations for building collaboration systems.
The trust model reflects this architecture:
This enables rich integrations but creates a centralized trust boundary where the platform provider ultimately controls the collaboration environment.
Secure messaging systems address the trust limitations of centralized collaboration platforms by implementing end-to-end encryption (E2EE), ensuring that only communicating participants can access message content.
Examples include Signal, Threema, and Element, all built on the Matrix ecosystem.
However, when SDKs are exposed by these systems, they typically function as client libraries for interacting with the messaging network rather than development platforms.
Common characteristics include:
While encryption is often strong, these SDKs generally assume that developers are building messaging clients or integrations, not new collaboration systems.
As a result:
The outcome is that these secure messaging platforms provide secure communication tools, but not necessarily a secure collaboration infrastructure for developers.
Between these two models lies a fundamental gap:
|
Model |
Developer Role |
Security Model |
Ecosystem Capability |
|
Mainstream collaboration platforms |
Extend an existing platform |
Server-trusted |
Large integration ecosystems |
|
Secure messaging applications |
Build messaging clients |
End-to-end encrypted |
Limited extensibility |
|
Wire SDK |
Build collaboration systems |
End-to-end encrypted infrastructure |
Secure collaboration ecosystem |
The Wire SDK addresses this gap by embedding the core cryptographic and collaboration infrastructure directly into the developer runtime.
The Wire Integration SDK fundamentally differs from typical messaging SDKs because it provides the underlying runtime required to build applications that operate inside secure collaboration environments, not just APIs to access one.
At its core, the SDK integrates:
Rather than interacting with a messaging service, developers interact with a secure collaboration runtime embedded in their application stack.
Wire Apps (created with the SDK) not only work in isolation within Wire but can also be used to "bridge" Wire and external services. Wire customers and partners can have their own software/automation, anddd the SDK allows events to go externally into Wire conversations, and vice versa.
A critical enabler of this model is Messaging Layer Security (MLS). MLS was designed specifically to support secure, scalable group messaging with strong cryptographic guarantees, including:
Implementing MLS correctly requires complex state management involving key trees, group membership changes, and automated rekeying. The Wire Integrations SDK encapsulates this complexity within the runtime. Developers, therefore, interact with secure collaboration primitives rather than cryptographic protocols, while still inheriting the full security guarantees of MLS.
Because the SDK manages the full cryptographic lifecycle, it effectively acts as a secure collaboration runtime embedded in applications. Key capabilities include:
The SDK automatically manages:
Applications can subscribe to collaboration events such as:
These events enable workflow automation and application logic to operate inside the encrypted collaboration environment. By subscribing to these events, you can trigger your application logic in an automated way. You can learn more about the SDK architecture at dev.wire.com/architecture.

By combining cryptographic infrastructure, identity primitives, and event-driven collaboration logic, the Wire Integrations SDK enables something that typical messaging SDKs cannot: secure collaboration ecosystems.
Multiple applications can interact within the same encrypted environment, including:
All participants operate within the same MLS-secured collaboration groups, sharing a common trust model enforced by the SDK.
This allows organizations to build ecosystems where collaboration services interact without exposing sensitive data to centralized infrastructure.
This architectural approach changes the role of developers. Instead of choosing between:
Developers can now build applications and services that operate natively inside Wire’s secure collaboration environment. The Wire SDK therefore transforms secure messaging from a feature of communication software into a foundational layer for building secure collaborative systems.
See our Wire Integrations SDK support page for more information.
Tech marketeer. I like readin' and writin' about cloud, data, networking, monitoring, DevOps.
Wire introduces a seamless upgrade process from personal to Teams accounts, offering enhanced collaboration features and invisible end-to-end...
Discover the Wire Integrations SDK, now live in production, enabling teams to build secure, end-to-end encrypted apps for automation and AI within...

Discover in a quick call how Wire enables secure, compliant, and seamless collaboration for your organization, without compromising on usability or control.